Threat detection boosted with AI
Posted on
Insider is the biggest risk
Why is our engineer working in the middle of the night? Shouldn’t he be at home, fast asleep? And why is he uploading all that data? But what if it isn’t our engineer at all?
The credentials are his valid credentials, but the actions and their timing seems very unlike him. Something is not right and this should be checked. His credentials may have been stolen and they may be used by a hacker, entering your system during off-duty hours to remain undetected. Or it could actually be our engineer himself and the insider risk may just have become reality for you. In fact, insider risk is one of the main cyber security concerns at the moment.
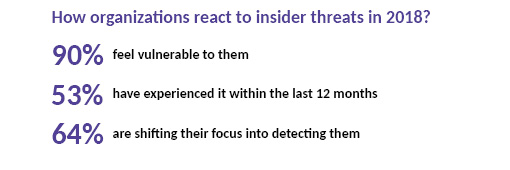
Insider risk facts from CA Technologies research.
AI to recognize suspicious behaviour
For you and me, the engineer’s strange behavior is easy to spot but to a traditional cyber security system, it might not be alerting. Traditional firewalls are necessary building blocks of overall security but they are unable to stop traffic that appears legitimate. An advanced hacker or a malicious insider will be able to leverage this fact to escape detection for long periods of time. Many breaches are never detected. To fight this, we have built a threat detection solution that combines our PreScope® sensors with machine learning AI.
Monitoring traffic to distinguish normal from the abnormal
Our PreScope sensors have the ability to monitor real-time traffic and provide continuous statistics on traffic and alerts for detected security threats. They can uncover traffic details down to packet level to provide information on what IP addresses are communicating, when and for how long, and how much data is being transferred. In order to detect threats, the sensors need information on what to look for. This information can come from a threat information platform, however, a platform can only have information on known threats. Could we teach the sensor to understand what is normal, and then detect the abnormal?
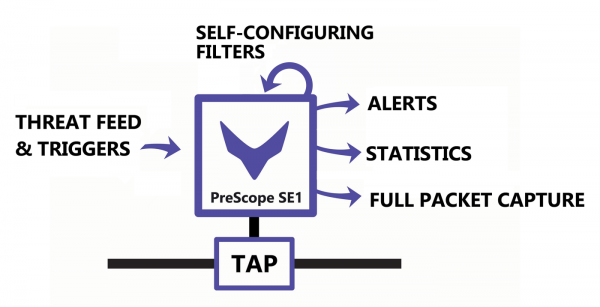
The PreScope sensor monitors traffic based on threat intelligence
Combinining sensors with AI capability
We humans can naturally distinguish normal from abnormal. To bring the human learning capability into threat detection, we have included AI expertise from CAP Data Technologies in our PreScope environment.
“Acquisition of new threat fingerprints requires a high level of know-how. The growing number of data and its threats makes the manual creation of fingerprints a slow and therefore expensive process. Our AI project has been able to significantly improve this situation by teaching artificial intelligence “CAP Anomaly Spotter” to identify probable threats and create new fingerprints. These are then set to our PreScope® to get the anomaly data so that human analytics can use it for post-verification if necessary“, says Dipti Adhikari, our Head of Engineering.
How is this done in practice? “CAP Anomaly Spotter’s several machine learning components observe the users’ behavior. With the rich data provided by PreScope®, we can find abnormal events in the network and inform the system to inspect these connections more closely,” explains Tuomo Sipola, Ph.D., CEO of CAP Data Technologies.
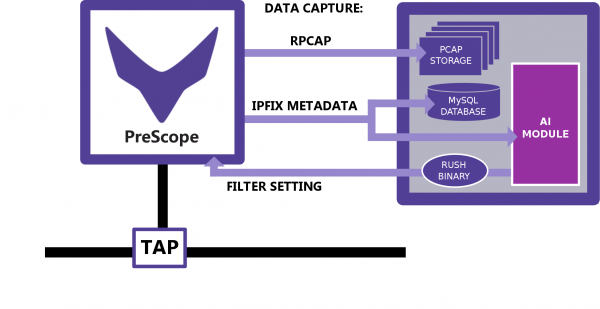
The above diagram shows how we combine the PreScope® sensor with CAP Anomaly Spotter. The sensor constantly monitors the traffic and sends the IPFIX metadata, a type of compressed information on traffic, to CAP Anomaly Spotter. If the AI finds something that might be a security threat, it updates PreScope® filters to better match the situation.
Detecting anomalies in the traffic
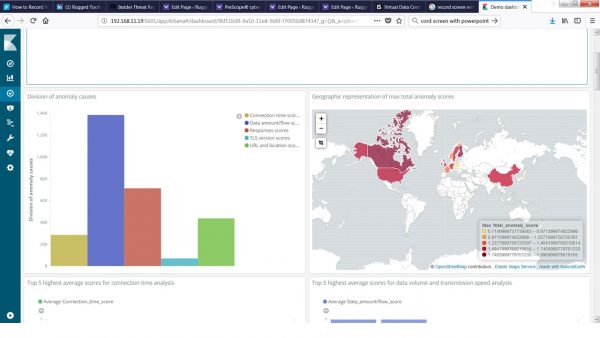
The system delivers information on what anomaly causes were detected most frequently, and also shows a map of the top locations from where the anomalies originated. You can delve deeper into a specific anomaly occurrence by clicking on it to see where its origin and details.

The results of the integration prove the capabilities of both the PreScope sensor and the Anomaly spotter, and that when combined, they are able to boost threat detection especially in the case of threats that might by overlooked by current security systems.
The research work on the integration has been carried out in a project backed by BusinessFinland. We at Rugged Tooling are honored to so-collaborate with CAP Data Technologies in bringing new intelligence into threat detection. To find out more about our PreScope platform, see the product page or contact us directly.